Every organization runs on access. Employees need to reach files, systems, and tools to get their work done. But if everyone can access everything, sensitive data quickly becomes exposed. That is where Identity and Access Management, or IAM, comes in.
IAM controls who can do what within a system. It makes sure the right people have the right access at the right time.
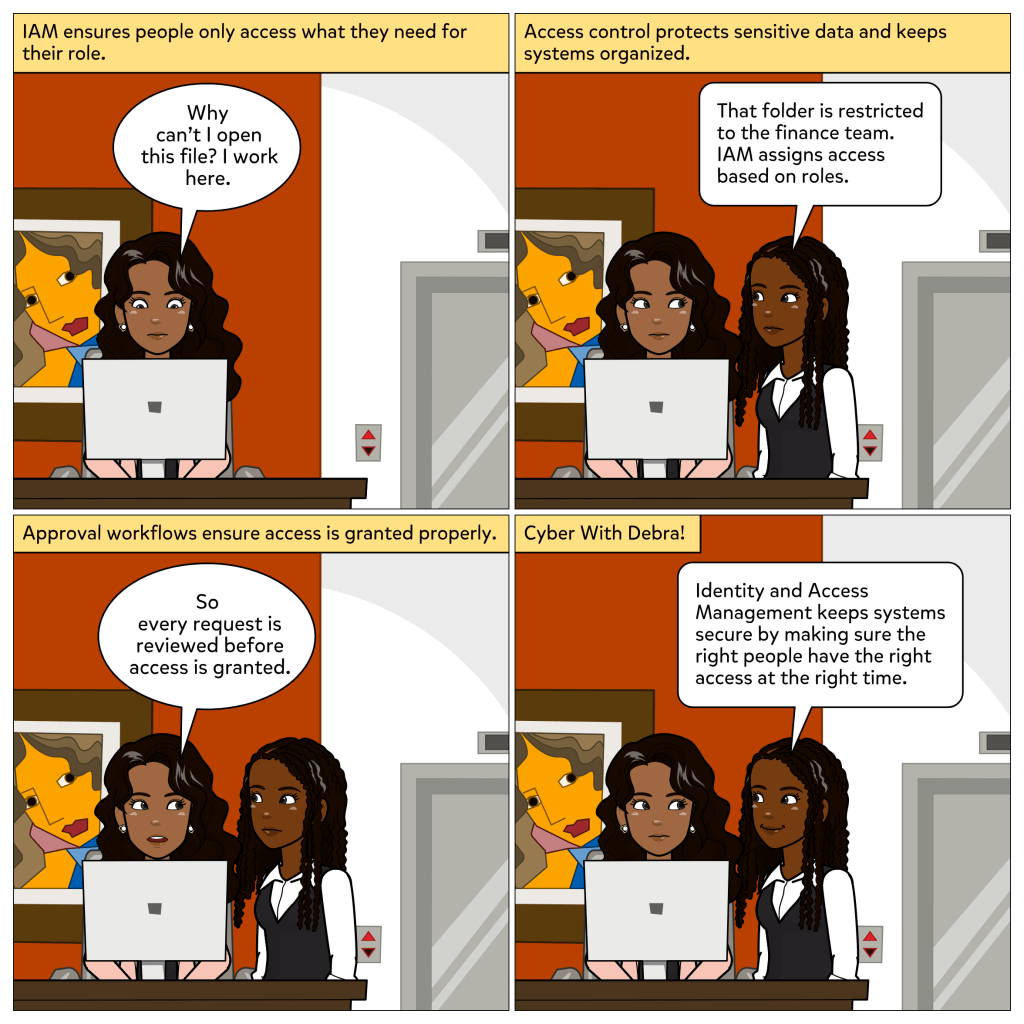
In this week’s comic, Michelle tries to open a folder and is surprised when access is denied. Debra explains that the folder is restricted to the finance team. IAM uses roles and permissions to make sure only authorized users can reach certain data. Each request is reviewed before access is granted, keeping systems secure and organized.
What IAM does
IAM gives organizations the structure to manage identities and permissions efficiently. It is the foundation of access control and accountability.
With IAM, organizations can:
• Authenticate users to verify who they are
• Authorize access to only what is needed for each role
• Manage permissions through approval workflows
• Monitor activity to detect unusual access patterns
Together, these steps help maintain visibility and trust across digital systems.
Why it matters
When access is too open, a single compromised account can cause major damage. IAM limits that risk by enforcing clear boundaries. It is especially important in industries like healthcare and finance, where privacy laws require strict control over who can view or modify sensitive information.
IAM also supports the principle of least privilege, meaning every user has exactly what they need to do their job and nothing more. That balance keeps security strong without slowing down productivity.
Everyday takeaway
Think of IAM like a building with secure rooms. Employees can enter the lobby freely, but only those with the right clearance can open specific doors. Each level of access protects something valuable inside.
Good security is not only about keeping outsiders away. It is also about managing trust within.
Thank you for reading. I hope you have subscribed. Let me know in the comments how your organization handles access control and user permissions. 🔑
Leave a comment