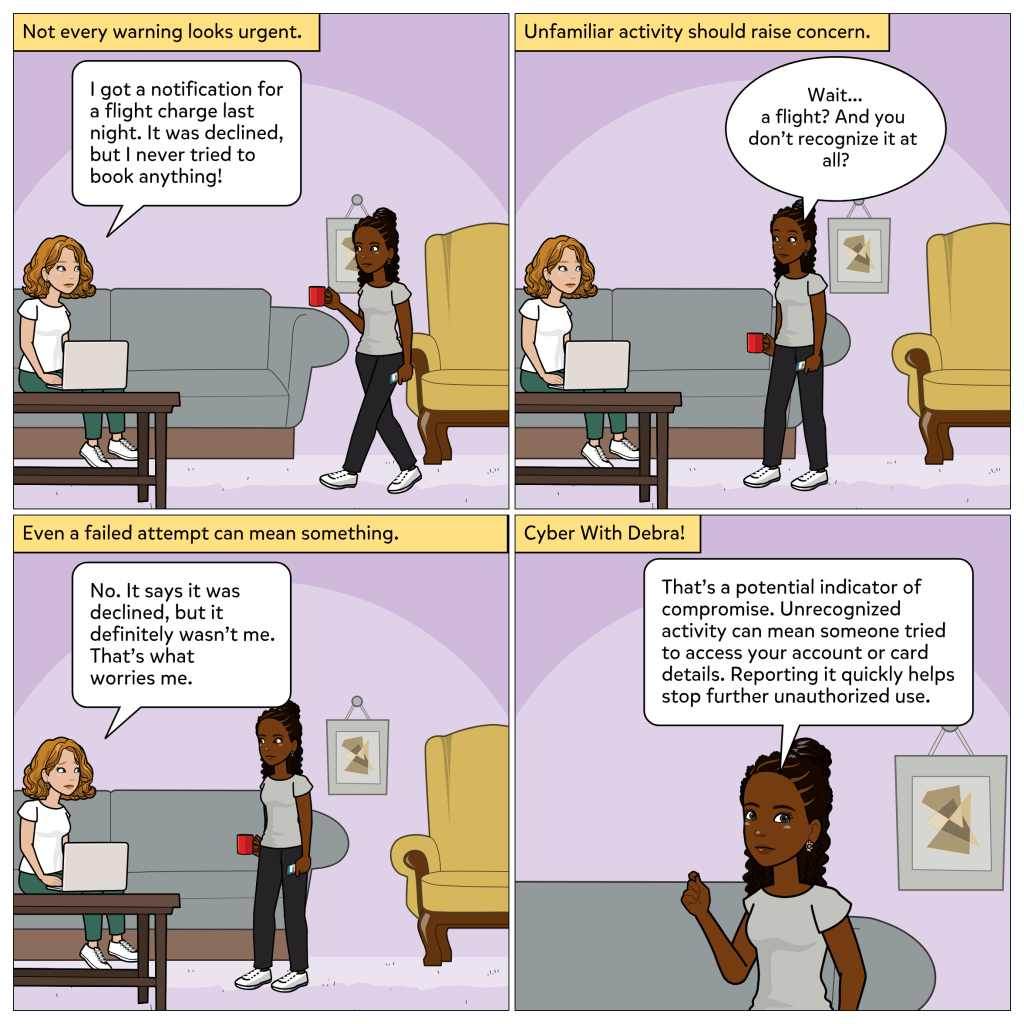
Not every security issue starts with something obvious.
Sometimes, it shows up as a small detail. A notification that does not seem urgent, but does not quite make sense either.
In this week’s comic, Sandy notices a charge for a flight that she never booked. It did not go through, but that is not what concerns her. What matters is that the attempt happened at all.
That moment is easy to overlook, but it points to something important.
What indicators of compromise really are
Indicators of compromise are signs that something may have been accessed, used, or targeted without permission.
In cybersecurity, these indicators often come from:
• unusual network traffic
• known malicious IP addresses
• unexpected file activity or hashes
• anomalous login behavior
But they do not only exist in technical systems. They also show up in everyday situations as activity that does not match what you expect.
At their core, indicators of compromise are about recognizing when something does not add up.
Why it matters
Attackers do not always succeed on the first try. Sometimes, their activity appears as failed attempts, unusual patterns, or small inconsistencies.
Those early signals are often the only warning before something more serious happens.
Recognizing them early can:
• prevent unauthorized access
• stop repeated attempts
• reduce potential impact
The difference is often not in the size of the issue, but in how quickly it is noticed and acted on.
Everyday takeaway
You do not have to wait for something to go wrong to take action.
If something does not look right, it is worth paying attention to.
Whether it is a declined charge, an unfamiliar login, or unexpected system behavior, those moments matter. Because in security, the signs are often there before the damage.
Thank you for reading. I hope you are subscribed. Have you ever noticed something small that did not seem right at first, but turned out to matter? Let me know in the comments 🔍